The F-21 buttonhole camera – as used by the Soviet Union, Europe, and North America in the early 1970s (International Spy Museum)
Despite ubiquitous surveillance and fancy gadgets, there are still simple, old-fashioned ways that spies and criminals can avoid detection, says Frank Swain.
In the wake of Edward Snowden’s revelations about the US National Security Agency’s activities around the globe, authorities in Russia and Germany declared they were investing in a foolproof counter-surveillance technology: mechanical typewriters. Patrick Sensburg, the head of the Bundestag inquiry into NSA spying, told a reporter from German TV programme Morgenmagazin the suggestion was “no joke”.
Is this the key to thwarting cybersnoopers? (Thinkstock)
Low-tech countermeasures to billion-dollar surveillance systems might seem outlandish, but old habits can be surprisingly effective. A variety of relatively unsophisticated tricks have helped spies, governments and criminals evade detection – right up to the present day.
A few years ago, for example, UK spies in Moscow were caught using afake rock in a park to hide electronic communication equipment. And when the FBI broke up a network of Russian sleeper agents operating in the US mainland in 2010, the court papers showed a remarkably lo-fi approach to communications. As well as bursts of data broadcast by shortwave radio – a technique dating back to World War II, the spies were reported to be using invisible ink, the same technique millions of schoolchildren use to hide their secrets.

Fake rocks are still used for dead drops to conceal and pass sensitive information (International Spy Museum)
“Invisible ink has been used by US spy agencies since the time of the Revolution,” says Vincent Houghton, historian and curator of the International Spy Museum in Washington DC, US. “What makes it great is that it’s not just the message that is hidden, it’s the actual existence of the message that is hidden.” In fact, the US Central Intelligence Agency kept an invisible ink recipe written during World War I secret for over a hundred years, only declassifying it in 2011. It is a rather more sophisticated recipe than lemon juice: “Mix 5 drams copper acetol arsenate. 3 ounces acetone and add 1 pint amyl alcohol (fusil-oil). Heat in water bath — steam rising will dissolve the sealing material of its mucilage, wax or oil.”
“It’s somewhat cumbersome and messy,” says Houghton. “But if you need to go low-tech, and even today we sometimes do, it’s a pretty good way to go.”
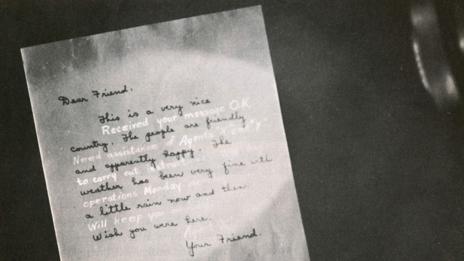
Many ways have been developed to conceal written messages (Science Photo Library)
Although many of Sensburg’s colleagues have ridiculed his suggestion of using mechanical typewriters, quarantining data from the internet has long been a cornerstone for security conscious individuals. Part of the reason Osama bin Laden was able to elude US authorities for so long was by staying offline. Instead, the al-Qaeda leader used a “sneakernet”. A subordinate would log into an anonymous email account from an internet cafe and copy the messages there onto a USB stick. The memory stick was taken to bin Laden, who would save his replies onto the memory stick to be sent out in the same manner.
To avoid imprinting emails with routing data, IP addresses and other tell-tale metadata, terrorists and spies alike use a second trick, saving the email to the drafts folder of a shared account without ever sending it. It’s a spycraft so popular that CIA director General David Petraeus himself used it to conduct an affair with his biographer, Paula Broadwell.

Listening devices, or ‘bugs’, from across the years (International Spy Museum)
Physically isolating a computer from the wider net – creating a so-called “air gap” – is another cheap and low-tech solution to evade billion-dollar surveillance systems that is practised by terrorists and state spies alike. However, an air gap can be difficult to maintain. Iran kept its uranium enrichment facilities air gapped, but the Stuxnet virus was able to cripple the all-important centrifuges after infected USB drives discarded by spies were plugged in by oblivious workers. Recent research from Berlin-based cyber-security experts Karsten Nohl and Jakob Lell suggests a new level of threat. A USB device that appears completely empty can still contain malware, even when formatted, say Nohl and Lell, and there is no practical way to defend against this.
Air gaps can also be crossed by sufficiently cunning programs, which could in principle be used by surveillance agencies to gain access to computer networks and collect information. Last year, security researcher Dragos Ruiu reported evidence that a virus had managed to jump the air gap in his laboratory. It was later confirmed the malware was spreading by high-frequency sounds passed between the speakers of an infected machine and the microphone of its next victim. Recommendations for keeping communications and databases secure now include gumming the microphone and USB sockets with glue.

The Stuxnet virus wreaked its havoc after infected USB drives were used by oblivious workers (Getty Images)
Architectural solutions to spyware also popped up in East Germany during the Cold War. “Intelligence wanted a low-tech and low-budget method to ensure its highest-level meetings were unbugged,” explains Houghton. “They decided the best way to do this was to build furniture out of transparent plastic, so that a bug would be easily spotted.” Twinned with sound dampening rooms and white noise generators, the Stasi agents could be confident that their discussions were not privy to eavesdroppers.
‘One-time pads’ are another low-tech trick that have stood the test of time. These are ciphers that are used just once before being destroyed. Such a pad might be a string of random numbers, each of which is used to move a letter in the message a corresponding number of places forward or backward in the alphabet. “Since it is random, and you’ve only used it once, you give the crypto guys nothing to work with and thus the code is unbreakable,” says Houghton. “It is still the only unbreakable code system ever created.”

German typewriter sales are higher than at any time in the past two decades (Getty Images)
Naturally, old techniques are by no means foolproof. Countermeasures exist for these as much as for hi-tech tricks – even one-time pads can be cracked if not used properly. And the reality is that no government agency is likely to scrap their computers and hi-tech equipment and return to the pre-electronic age. Sensburg’s call for a return to typewriters may well be an eye-catching exercise to appease the public that the German authorities are responding to perceived breaches in their secrecy.
Still, it may be reassuring to some that even today’s massive global surveillance operation could still be scuppered by see-through chairs and invisible ink.
News Source: http://www.bbc.com/future/story/20140807-the-best-low-tech-spy-tricks
